
The smartphones and mobile devices have become an essential over the time. We always carry them wherever we go. However, with the passage of time, as the usage of the smartphone increases, the demand for high performance also arises. The smartphone, tablets and handheld devices’ industry have witnessed tremendous amount of progress and innovation. One thing that everyone always complaint about is the battery of the smartphones. These days some high-end smartphones are even equal to laptops with their computing powers and capabilities.
However, one thing is common among almost all smartphones that most of them last only for a day at full charge. We all faced situations when we had to make a very important call and our phone dies or we are out of office/home and our phone displays low battery warning. In such situations sighting a public mobile charging station is a great relief. That is the reason more and more businesses are offering public mobile charging stations, some are offering for free and some are offering for nominal fees.

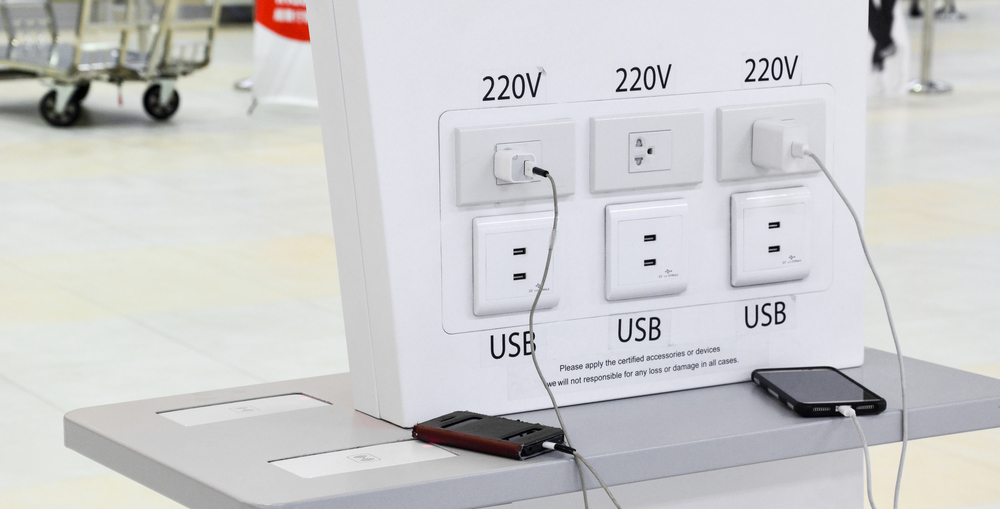
Here in Dubai and all around the UAE the mobile charging stations are very common. Most of the people never think that a mobile charging station could pose a threat too. However, security experts have warned about possible malware threats from public mobile charging stations. A perpetrator can possibly install a malicious program in your smartphone through mobile charging stations.
This is often referred to as ‘Juice Jacking’ and according to FCC the perpetrators can use a special purpose dirty USB device in order to gain access to someone’s phone. They can collect valuable personal data, user accounts, financial data and much more which either they can use to orchestrate more criminal activities or they can sell the data to other cyber criminals.
See Also: Why Mobile Charging Stations Are Essential in Waiting Rooms?
What is Juice Jacking?
The juice jacking is a technique to install malware on the smartphones, tablets, and other devices. This malware can automatically look up at most obvious places to steal the user identity, user accounts, their banking details, email and social media accounts and much more. Basically the idea was first presented in the DEF CON 2011. The DEF CON is a security conference where ethical-hackers security experts and programmers held a conference and present their idea with like-minded people.
The Juice Jacking technique is developed to exploit the natural process of a USB device. Everyone knows the USB port at their smartphone have two functions, one is to charge the device and the other is to connect it with a PC or Laptop to transfer the data. That is what the Juice Jacking technique exploit, when we connect our phone with a charger we also provide possibility to transfer the data. That is how the Juice Jacking works.
See Also: Cell Phone Charging Station Guide for Businesses
Should I worry About Juice Jacking?
Now in 2022 the smartphones have become way too smart and protected also. Now a days all smartphone popup a warning/permission message whenever they are connected to a USB post capable of data transferring. As I mentioned above the Juice Jacking was presented in DEF CON, however, we still haven’t receive a single report of someone data is stolen through Juice Jacking method in real-life. The smartphones manufacturers are well aware of these loopholes and they have taken concrete steps to prevent someone getting unauthorized access to you data.
So, no, you don’t have to worry at all. The Juice Jacking is long gone, it never proven to work in real-life scenarios, and since past 7, 8 years all smartphone manufacturers have introduced a several security layers to prevent such exploits. Just be cautious when using a mobile charging station, especially the free ones, when you plug-in your device wait for a few seconds and if a popup or notification appears on screen asking you to accept or cancel data transfer in any mode, immediately remove your device. But the chances of getting affected by Juice Jacking are slim to none. So, no need to worry about it.
See Also: Benefits of Mobile charging stations at Shopping Malls

How would You Know if you are Juice Jacked or any other Malware has Infected Your Device?
There are so many different methods to check and examine a smartphone tablet or smart device to tell if it is infected by a malware. However, all those methods require at least some level of technical understanding and knowhow which is not so common. So here are some very common signs that everyone can notice if they look closely:
 |
Rise in Battery Consumption:A sudden rise in battery consumption is one of the most common sign that you are juice jacked or any other malicious virus have infected your device. These malwares run in the background, so you won’t be able to notice them, however, they will keep utilizing your processor which will consume a lot of battery. |
 |
Poor Performance:The smartphones, tablets or smart devices which got infected by Malware, Viruses or Trojans got slower, and keep freezing as all these processes are running in the background, sometimes it keep restarting itself. One can easily notice if the application they use more frequently are slower than earlier. |
 |
Changes in Device Settings:You will have to look closely to notice if your device setting are getting changed automatically or you are changing settings but they are reverting back automatically after some time. The apps and their settings are also important to monitor. You might also notice several apps keep crashing without any reason. |
 |
Other Unusual Activities:The most common abnormalities caused by the malwares and viruses that everyone can easily notice are increased heat at the back of the device, as these processes keep heating up the processors and other chips. Mostly in idle state the screen is completely dark, if your phone’s screen start flashing just for a sec or two then there might be something running in the background. |
 |
Data Usage:Now a days almost every smartphone, tablet or smart device have in-built data usage monitoring tools, which help you understand which applications are using what amount of data, etc. You are also aware of your regular data usage, so if without any additional activity you notice unusual increase in the data usage, then most likely it could be a malware or Trojan virus using your data to connect to its source. So, closely monitor your data consumption. |
Mostly the hacked devices got unnoticed as most of us are not aware of these signs. Sometimes even if we notice anything unusual we think that the device might be broken or if it is older than 6 – 8 months, the first thing that usually came to ones’ mind is that the device might have too much data in it which is slowing it down or causing these unusual behavior. Most of us just factor reset the device which mostly resolve a lot of problems.
What can I do if my Smartphone got Juice Jacked or Hacked?
First of all make sure you got one or more than one of the above mentioned signs. If you are certain that you got juice jacked or even if any other malware, virus or Trojan have infected your device, here are a few things you can easily do to prevent any more damage:
- Immediately turn off your Data and WiFi, make sure it got disconnected from the internet
- Obviously everyone have important data on their smartphones, so take a backup of your data
- Both Android and Apple offer desktop applications to perform backups, reset, update, etc. features, better to use your brand’s desktop app
- It is a plus point if the PC/Laptop you are connecting your device with have a good Antivirus on it
- Take backup of your data and factory reset your device
- Reset the passwords of all accounts that were signed-in on the infected device
- Setup your factory reset device by signing-in with only necessary accounts/emails/IDs to avoid further damage
- Install an Antivirus program and scan your device with it
- Monitor your smartphone, tablet or smart device for a couple of days, and see if any abnormality appears again or not
- If not, then it is save to restore your data and start using your device regularly
- If any sign appears again, then contact a professional to help you out

There are several ways to get virus, malware or Trojans, however, the smartphone charging station is considered to be the safest till date. Now a days, the smartphone charging station vendors have made them more secure by adding charging-only cables, which are completely incapable of data transfer. Hence no one could exploit them. However, there has been some devices which are used by most sophisticated cyber criminals, these devices usually look like additional connectors, if you notice something like this, do not connect your phone on it, and immediately notify the relevant authorities.
Conclusion
The 2021 and 2022 witnessed some high-level corporate hacks, which involved huge corporations and the worldwide media made them popular which lead to several awareness campaigns and a lot many people learned about those cyber-criminals and their methods, etc. However, where these incidents help creating awareness they also raised fear. That is why the mobile charging stations have become a new debate these days. The idea of getting hacked through your smartphone or tablet in itself is freighting and when we start reading blogs covering Juice Jacking and smartphone charging stations, it become even worse. However, as I mentioned the Juice Jacking is almost obsolete but still people are concerned. Here in Dubai and all around the UAE the government take cyber-security very seriously, and have very strict policies against cyber-criminals.
When it comes to mobile charging stations, there is no harm in using them just be careful to see if anything is unusual. RSI Concepts is a leading smartphone charging station provider in Dubai, UAE. If you want to learn more about the subject or want us to provide you a customized mobile charging station please feel free to contact us through our Contact Us page or leave a comment in the comment box below and we will get in touch with you soon.
